Improve your health
Improve your health
Improve your health
23. Januar 2026
NIST Updates: What Health Apps Need to Know


The NIST Cybersecurity Framework 2.0, released in February 2024, introduces key updates that health app developers must understand to protect sensitive data and align with regulations like HIPAA. These updates address modern threats and simplify compliance processes. Key changes include:
New "Govern" Function: Highlights cybersecurity as a business risk, not just an IT concern.
Supply Chain Security: Focuses on managing risks from third-party services and APIs.
HIPAA Alignment: NIST SP 800-66 Rev. 2 maps HIPAA requirements to the updated framework, easing compliance efforts.
Expanded Reach: Now applicable to organizations of all sizes, including small health app developers.
New Tools: Resources like the CSF 2.0 Reference Tool and Quick-Start Guides support implementation.
With healthcare data breaches up 93% from 2018 to 2022, adopting NIST's framework is critical for safeguarding electronic protected health information (ePHI). The updates also prepare developers for stricter 2026 compliance standards, requiring annual risk assessments, multi-factor authentication, and robust data protection measures.
What Changed in NIST Cybersecurity Framework 2.0
Main Updates in Framework 2.0
The standout shift in Framework 2.0 is its expanded reach. While version 1.1 primarily targeted critical infrastructure like hospitals and power plants, the updated framework is designed to serve organizations of all sizes [6]. This means it's now just as relevant for a large healthcare system as it is for a small developer creating consumer health apps.
Another key addition is the introduction of a sixth core function, "Govern," which emphasizes that cybersecurity is not just an IT issue but a critical business risk that leadership must address [6]. NIST Director Laurie E. Locascio highlighted the flexibility of the new version:
"CSF 2.0, which builds on previous versions, is not just about one document. It is about a suite of resources that can be customized and used individually or in combination over time as an organization's cybersecurity needs change and its capabilities evolve" [6].
The updated framework also strengthens guidance on supply chain security, helping organizations better manage third-party risks [6]. Alongside these updates, NIST has rolled out resources like Quick-Start Guides aimed at small businesses and a CSF 2.0 Reference Tool. This tool allows developers to export outcomes in machine-readable formats and cross-reference them with over 50 other cybersecurity documents [6].
The healthcare sector has already embraced the framework extensively - 71% of healthcare organizations are using the NIST Cybersecurity Framework, with 57% identifying it as their primary security framework [7]. Organizations adopting the framework have also reported slower increases in cybersecurity insurance premiums year-over-year [7]. These updates make the framework more versatile while also simplifying compliance processes, such as those required under HIPAA.
How NIST 2.0 Works with HIPAA Security Rule
The expanded features in CSF 2.0 also make it easier to align with HIPAA compliance requirements. Enhanced mapping in the updated framework connects NIST outcomes directly to regulatory documents. For example, the CSF 2.0 Reference Tool includes a searchable catalog of "Informative References" that link to NIST SP 800-53, a resource frequently used to demonstrate compliance with the HIPAA Security Rule. This allows developers of health apps to address both NIST and HIPAA requirements using a single framework [6].
The new "Govern" function aligns with HIPAA's mandate for administrative safeguards and regular risk analysis by embedding cybersecurity into enterprise risk management [4][6]. Kevin Stine, Chief of NIST's Applied Cybersecurity Division, explained the broader vision:
"This update aims to make the framework even more relevant to a wider swath of users in the United States and abroad" [6][7].
For developers handling electronic protected health information (ePHI), this alignment reduces the complexity of managing multiple security frameworks, streamlining their compliance efforts.
How Health Apps Can Meet NIST Requirements
Risk Assessments and Vulnerability Management
The first step in meeting the HIPAA Security Rule is conducting a thorough risk analysis [8]. For developers of health apps, this involves identifying all electronic protected health information (ePHI) that your app creates, receives, maintains, or transmits. This includes data stored on servers, mobile devices, cloud platforms, or portable media. Start by mapping out where ePHI is stored. This can be done through document reviews and team interviews. Then, identify potential threats - whether they stem from human actions (intentional or accidental), natural disasters (like floods or earthquakes), or environmental factors. Evaluate your existing security measures, assess the likelihood of each threat exploiting a vulnerability, and determine the potential impact. This process helps assign risk levels effectively.
For smaller developers, tools like the HIPAA Security Risk Assessment (SRA) Tool from the Office of the National Coordinator (ONC) and the Office for Civil Rights (OCR) can simplify this process. Be sure to update your risk analysis whenever new features are added or after any incidents occur. These steps lay the groundwork for stronger authentication and data protection strategies.
Setting Up Multi-Factor Authentication and Audit Logging
Multi-factor authentication (MFA) is a key safeguard for protecting ePHI from unauthorized access under the HIPAA Security Rule [9]. MFA requires at least two verification methods, such as a password combined with a token or biometric identifier.
In July 2025, NIST finalized SP 800-63 Revision 4, following extensive feedback from nearly 6,000 public comments [11]. This updated guidance addresses modern threats like injection attacks, forged media, and deepfakes used in identity fraud. It also introduces synced passkeys, which improve both security and user experience.
Audit logging is another critical component for maintaining security. Logs help detect cybersecurity events and support incident response efforts. Your app should track and analyze activity in systems handling sensitive data, creating a clear accountability trail for investigating breaches and proving compliance. Developers can use the NIST HIPAA Security Toolkit Application to evaluate their MFA and audit logging measures [10]. For more detailed guidance on managing authenticators and ensuring digital identity assurance, refer to SP 800-63B-4 [11]. Together, MFA and audit logging strengthen the protection of sensitive data throughout its lifecycle.
Data Protection Best Practices
To safeguard ePHI, align your security program with the six core functions of NIST CSF 2.0: Identify, Protect, Detect, Respond, Recover, and Govern [13]. NIST Special Publication 800-66 Revision 2 provides detailed guidance on protecting ePHI at every stage - from creation to transmission [12].
Key measures include encrypting data at rest and in transit, implementing role-based access controls, and maintaining secure backups to recover from incidents like ransomware attacks. Use formal risk assessments to prioritize security efforts, focusing on the potential impact on patient data [12]. Automated monitoring systems under the "Detect" function are essential for identifying cybersecurity threats in real time. Additionally, a comprehensive recovery plan ensures business continuity in the face of disruptions [13].
"Adopting the NIST Cybersecurity Framework for healthcare is not just a measure of compliance; it's a strategic move toward ensuring the confidentiality, integrity, and availability of critical healthcare data" [13].
Monica McCormack, Compliance Copywriter and Editor at Compliancy Group
Finally, conduct a gap analysis with your IT team to identify areas where your current practices fall short of NIST recommendations. Implement role-based training to build a culture of security awareness and ensure your team is prepared to handle evolving threats [13].
How to Apply NIST SP 800-66 to Meet HIPAA Third-Party Risk Management Requirements
NIST Framework Functions for Health Apps
NIST Cybersecurity Framework Functions for Health Apps
NIST Functions vs. Health App Requirements
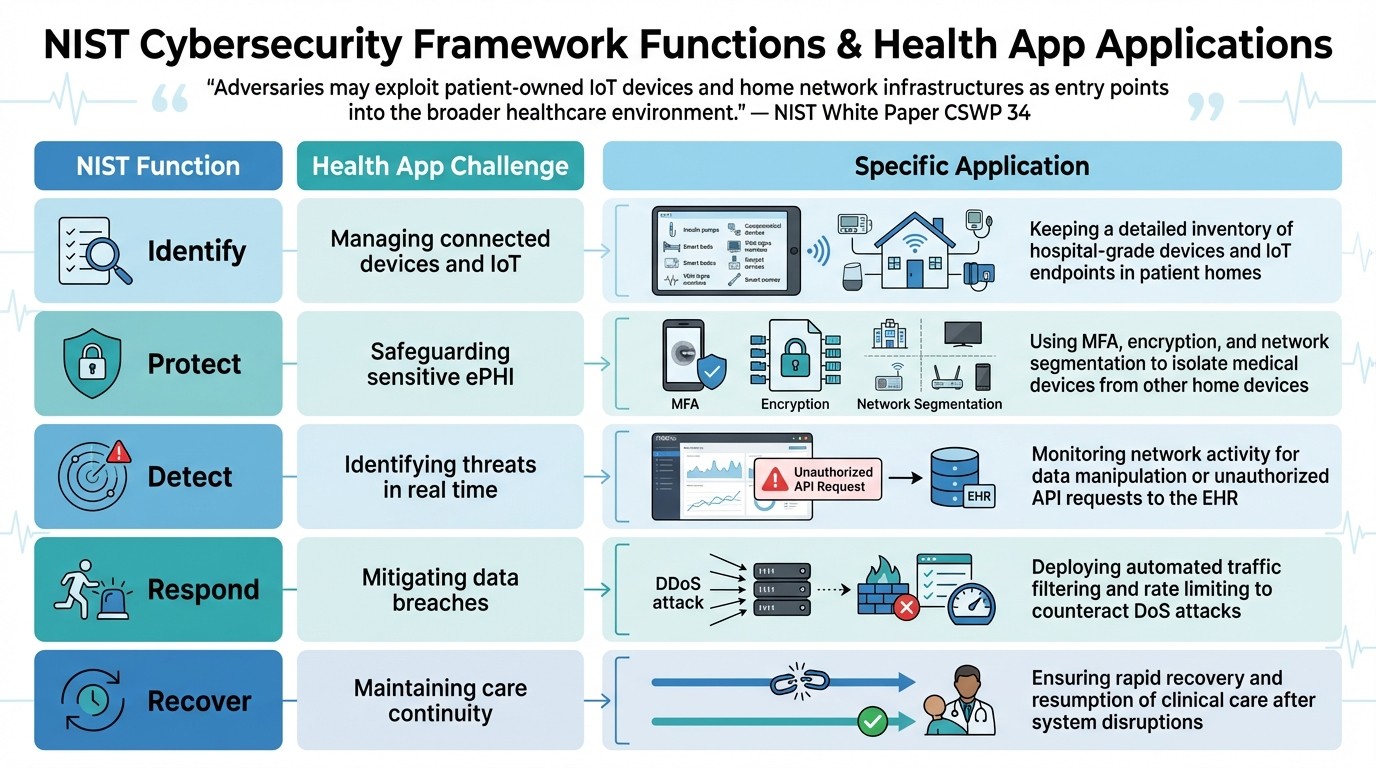
The NIST Cybersecurity Framework (CSF) 2.0 outlines five core functions - Identify, Protect, Detect, Respond, and Recover - designed to tackle the specific challenges faced by health apps. Unlike traditional enterprise systems, health apps often operate in complex environments like Hospital-at-Home setups. These settings combine hospital-grade devices with consumer IoT products, many of which fall outside centralized control [14]. The framework serves as a guide for addressing vulnerabilities in this mixed ecosystem of medical and consumer technologies.
Each function addresses a key area of risk. The Identify function focuses on cataloging every component that interacts with patient data. This includes hospital-grade biometric devices, third-party APIs, and even personal devices owned by patients.
The Protect function demands robust security measures, such as adopting Zero Trust architectures (as outlined in NIST SP 800-207). This involves continuous authentication for all users and devices accessing Electronic Health Records (EHRs). Additionally, network segmentation plays a critical role, isolating medical devices from other home network devices to prevent breaches through compromised IoT products like smart speakers.
"Adversaries may exploit patient-owned IoT devices and home network infrastructures as entry points into the broader healthcare environment." - NIST White Paper CSWP 34
The Detect function emphasizes real-time monitoring to spot anomalies, such as Distributed Denial of Service (DDoS) attacks or unauthorized API activities that could compromise patient data. The Respond function focuses on automated mitigation strategies, such as traffic filtering and rate limiting, to reduce disruptions to essential clinical services. Lastly, the Recover function prioritizes restoring system availability and predictability, ensuring patients continue to receive uninterrupted care.
The table below highlights how these NIST functions address specific challenges and applications in health apps:
NIST Function | Health App Challenge | Specific Application |
|---|---|---|
Identify | Managing connected devices and IoT | Keeping a detailed inventory of hospital-grade devices and IoT endpoints in patient homes |
Protect | Safeguarding sensitive ePHI | Using MFA, encryption, and network segmentation to isolate medical devices from other home devices |
Detect | Identifying threats in real time | Monitoring network activity for data manipulation or unauthorized API requests to the EHR |
Respond | Mitigating data breaches | Deploying automated traffic filtering and rate limiting to counteract DoS attacks |
Recover | Maintaining care continuity | Ensuring rapid recovery and resumption of clinical care after system disruptions |
Getting Ready for 2026 Compliance: A Step-by-Step Plan
The December 2024 Notice of Proposed Rulemaking has set the stage for stricter auditing and technical requirements for health apps by 2026 [15]. With the shift from vague "reasonable and appropriate" standards to clear, time-bound mandates, organizations need to act now. Here's a practical plan to prepare for these changes.
Running a Complete Risk Analysis
Start with a thorough risk analysis of all e-PHI (electronic Protected Health Information) stored, transmitted, or accessed via mobile devices, cloud platforms, and other media [8]. The proposed 2026 rules emphasize maintaining an up-to-date asset inventory and network map that tracks the flow of e-PHI, refreshed at least annually [15]. Identify potential threats - whether natural, human, or environmental - and evaluate their likelihood and potential impact [8].
The new regulations also require annual compliance audits, biannual vulnerability scans, yearly penetration tests, and the ability to restore data and systems within 72 hours [15]. These measures, which were previously considered optional, are now mandatory for nearly all cybersecurity practices [15].
Once risks are identified, implement robust access controls and establish continuous monitoring systems to mitigate vulnerabilities effectively.
Role-Based Access and Continuous Monitoring
Implement Zero Trust principles to enforce role-based access controls, treating every login attempt as potentially untrusted, regardless of its origin [17]. The HHS Office for Civil Rights has increased enforcement efforts, announcing 10 settlements in the first five months of 2025 alone, many of which stemmed from failures in basic risk analysis [17]. Multi-factor authentication (MFA) is now a requirement for all administrative and critical system access under the updated HIPAA Security Rule proposals [17].
For health apps operating in cloud environments, it's crucial to securely configure Identity and Access Management (IAM) policies, manage application-level credentials, and enforce strict authorization measures [16]. Network segmentation is another key strategy - separating clinical and medical device networks from general IT and guest networks can help contain potential breaches and limit lateral movement by attackers [17]. To maintain continuous vigilance, establish a Security Operations Center (SOC) or partner with a Managed Detection and Response (MDR) service to monitor for signs of data exfiltration or unusual access patterns [17].
Conclusion
The NIST Cybersecurity Framework 2.0 introduces a flexible, risk-based approach that’s crucial for health apps navigating today’s complex cybersecurity landscape. With NIST SP 800-66 Rev. 2 aligning HIPAA Security Rule elements to CSF 2.0 subcategories, this framework has become a key resource for meeting compliance requirements and building user confidence [1]. As Jeff Marron, a cybersecurity specialist at NIST, explained:
"The revision is more actionable so that health care organizations can improve their cybersecurity posture and comply with the Security Rule" [1].
The surge in healthcare-related cyberattacks highlights the importance of protecting sensitive data. For health apps managing electronic protected health information, safeguarding the confidentiality, integrity, and availability of this data is non-negotiable. The addition of the "Govern" function in CSF 2.0 emphasizes that cybersecurity is not just an IT issue - it’s a critical component of broader enterprise risk management [2][3]. This makes strong cybersecurity practices both a regulatory requirement and a strategic advantage.
Looking ahead, updates to the IR 8286 series by December 2025 will fully align with CSF 2.0, while tools like SP 800-70r5 will simplify compliance reporting through automation [3]. This framework also addresses emerging technologies that are transforming healthcare, such as AI-powered health tools and IoT devices used in home care [5].
By taking steps like conducting thorough risk assessments and implementing continuous monitoring, health apps can align their technical controls with regulatory standards. Tools like the CSF 2.0 Reference Tool and Quick-Start Guides provide a clear path to updating security measures for 2026 compliance. As NIST emphasizes:
"The CSF does not prescribe how outcomes should be achieved. Rather, it links to online resources that provide additional guidance on practices and controls that could be used to achieve those outcomes" [2].
This flexible, outcome-driven approach allows health apps to customize their security strategies based on their unique risk profiles, all while meeting the rigorous standards of the future.
For apps like Healify, adopting these practices isn’t just about meeting regulations - it’s about earning user trust and safeguarding sensitive health data in an increasingly digital world.
FAQs
What does the new 'Govern' function in NIST CSF 2.0 mean for health app developers?
The updated 'Govern' function in NIST CSF 2.0 places a stronger emphasis on cybersecurity governance, aligning risk management with an organization's broader objectives while promoting accountability. For health app developers, this means establishing clear oversight of cybersecurity efforts, refining how risks are identified and mitigated, and adhering to new governance standards.
This shift underscores the need to weave cybersecurity into the fabric of business strategies - an essential move for health apps managing sensitive data such as biometrics and medical records. Developers must take proactive steps to protect user information, ensuring their operations remain transparent and accountable.
What should small health app developers do to meet NIST and HIPAA security requirements?
To comply with NIST and HIPAA security standards, small health app developers should prioritize a few essential security practices. Start by familiarizing yourself with the NIST Cybersecurity Framework and the latest updates to SP 800-66r2, which offer actionable steps for meeting the HIPAA Security Rule requirements. Regular risk assessments are a must - identify weaknesses, address them promptly, and implement safeguards to secure electronic protected health information (ePHI).
Another critical step is aligning your security protocols with the crosswalk between the HIPAA Security Rule and the NIST framework. This ensures your app includes essential protections like data encryption, access controls, and incident response plans. Staying informed on regulatory changes and updated guidance is key to keeping your app compliant and protecting user data effectively.
Why is multi-factor authentication so important for health apps under the updated NIST guidelines?
Multi-factor authentication (MFA) plays a crucial role in securing health apps by adding an extra layer of protection. This makes it far more difficult for unauthorized individuals to gain access to sensitive health data. It also aligns with the updated NIST Cybersecurity Framework, which prioritizes safeguarding personal information and managing cybersecurity risks effectively.
MFA works by requiring users to confirm their identity through multiple verification methods - like entering a password and then using a code sent to their phone. This significantly lowers the risk of data breaches. For health apps that handle highly sensitive information, such as biometrics or medical records, implementing MFA isn't just a smart move - it’s essential for maintaining user trust and meeting today’s security requirements.
Related Blog Posts
The NIST Cybersecurity Framework 2.0, released in February 2024, introduces key updates that health app developers must understand to protect sensitive data and align with regulations like HIPAA. These updates address modern threats and simplify compliance processes. Key changes include:
New "Govern" Function: Highlights cybersecurity as a business risk, not just an IT concern.
Supply Chain Security: Focuses on managing risks from third-party services and APIs.
HIPAA Alignment: NIST SP 800-66 Rev. 2 maps HIPAA requirements to the updated framework, easing compliance efforts.
Expanded Reach: Now applicable to organizations of all sizes, including small health app developers.
New Tools: Resources like the CSF 2.0 Reference Tool and Quick-Start Guides support implementation.
With healthcare data breaches up 93% from 2018 to 2022, adopting NIST's framework is critical for safeguarding electronic protected health information (ePHI). The updates also prepare developers for stricter 2026 compliance standards, requiring annual risk assessments, multi-factor authentication, and robust data protection measures.
What Changed in NIST Cybersecurity Framework 2.0
Main Updates in Framework 2.0
The standout shift in Framework 2.0 is its expanded reach. While version 1.1 primarily targeted critical infrastructure like hospitals and power plants, the updated framework is designed to serve organizations of all sizes [6]. This means it's now just as relevant for a large healthcare system as it is for a small developer creating consumer health apps.
Another key addition is the introduction of a sixth core function, "Govern," which emphasizes that cybersecurity is not just an IT issue but a critical business risk that leadership must address [6]. NIST Director Laurie E. Locascio highlighted the flexibility of the new version:
"CSF 2.0, which builds on previous versions, is not just about one document. It is about a suite of resources that can be customized and used individually or in combination over time as an organization's cybersecurity needs change and its capabilities evolve" [6].
The updated framework also strengthens guidance on supply chain security, helping organizations better manage third-party risks [6]. Alongside these updates, NIST has rolled out resources like Quick-Start Guides aimed at small businesses and a CSF 2.0 Reference Tool. This tool allows developers to export outcomes in machine-readable formats and cross-reference them with over 50 other cybersecurity documents [6].
The healthcare sector has already embraced the framework extensively - 71% of healthcare organizations are using the NIST Cybersecurity Framework, with 57% identifying it as their primary security framework [7]. Organizations adopting the framework have also reported slower increases in cybersecurity insurance premiums year-over-year [7]. These updates make the framework more versatile while also simplifying compliance processes, such as those required under HIPAA.
How NIST 2.0 Works with HIPAA Security Rule
The expanded features in CSF 2.0 also make it easier to align with HIPAA compliance requirements. Enhanced mapping in the updated framework connects NIST outcomes directly to regulatory documents. For example, the CSF 2.0 Reference Tool includes a searchable catalog of "Informative References" that link to NIST SP 800-53, a resource frequently used to demonstrate compliance with the HIPAA Security Rule. This allows developers of health apps to address both NIST and HIPAA requirements using a single framework [6].
The new "Govern" function aligns with HIPAA's mandate for administrative safeguards and regular risk analysis by embedding cybersecurity into enterprise risk management [4][6]. Kevin Stine, Chief of NIST's Applied Cybersecurity Division, explained the broader vision:
"This update aims to make the framework even more relevant to a wider swath of users in the United States and abroad" [6][7].
For developers handling electronic protected health information (ePHI), this alignment reduces the complexity of managing multiple security frameworks, streamlining their compliance efforts.
How Health Apps Can Meet NIST Requirements
Risk Assessments and Vulnerability Management
The first step in meeting the HIPAA Security Rule is conducting a thorough risk analysis [8]. For developers of health apps, this involves identifying all electronic protected health information (ePHI) that your app creates, receives, maintains, or transmits. This includes data stored on servers, mobile devices, cloud platforms, or portable media. Start by mapping out where ePHI is stored. This can be done through document reviews and team interviews. Then, identify potential threats - whether they stem from human actions (intentional or accidental), natural disasters (like floods or earthquakes), or environmental factors. Evaluate your existing security measures, assess the likelihood of each threat exploiting a vulnerability, and determine the potential impact. This process helps assign risk levels effectively.
For smaller developers, tools like the HIPAA Security Risk Assessment (SRA) Tool from the Office of the National Coordinator (ONC) and the Office for Civil Rights (OCR) can simplify this process. Be sure to update your risk analysis whenever new features are added or after any incidents occur. These steps lay the groundwork for stronger authentication and data protection strategies.
Setting Up Multi-Factor Authentication and Audit Logging
Multi-factor authentication (MFA) is a key safeguard for protecting ePHI from unauthorized access under the HIPAA Security Rule [9]. MFA requires at least two verification methods, such as a password combined with a token or biometric identifier.
In July 2025, NIST finalized SP 800-63 Revision 4, following extensive feedback from nearly 6,000 public comments [11]. This updated guidance addresses modern threats like injection attacks, forged media, and deepfakes used in identity fraud. It also introduces synced passkeys, which improve both security and user experience.
Audit logging is another critical component for maintaining security. Logs help detect cybersecurity events and support incident response efforts. Your app should track and analyze activity in systems handling sensitive data, creating a clear accountability trail for investigating breaches and proving compliance. Developers can use the NIST HIPAA Security Toolkit Application to evaluate their MFA and audit logging measures [10]. For more detailed guidance on managing authenticators and ensuring digital identity assurance, refer to SP 800-63B-4 [11]. Together, MFA and audit logging strengthen the protection of sensitive data throughout its lifecycle.
Data Protection Best Practices
To safeguard ePHI, align your security program with the six core functions of NIST CSF 2.0: Identify, Protect, Detect, Respond, Recover, and Govern [13]. NIST Special Publication 800-66 Revision 2 provides detailed guidance on protecting ePHI at every stage - from creation to transmission [12].
Key measures include encrypting data at rest and in transit, implementing role-based access controls, and maintaining secure backups to recover from incidents like ransomware attacks. Use formal risk assessments to prioritize security efforts, focusing on the potential impact on patient data [12]. Automated monitoring systems under the "Detect" function are essential for identifying cybersecurity threats in real time. Additionally, a comprehensive recovery plan ensures business continuity in the face of disruptions [13].
"Adopting the NIST Cybersecurity Framework for healthcare is not just a measure of compliance; it's a strategic move toward ensuring the confidentiality, integrity, and availability of critical healthcare data" [13].
Monica McCormack, Compliance Copywriter and Editor at Compliancy Group
Finally, conduct a gap analysis with your IT team to identify areas where your current practices fall short of NIST recommendations. Implement role-based training to build a culture of security awareness and ensure your team is prepared to handle evolving threats [13].
How to Apply NIST SP 800-66 to Meet HIPAA Third-Party Risk Management Requirements
NIST Framework Functions for Health Apps
NIST Cybersecurity Framework Functions for Health Apps
NIST Functions vs. Health App Requirements
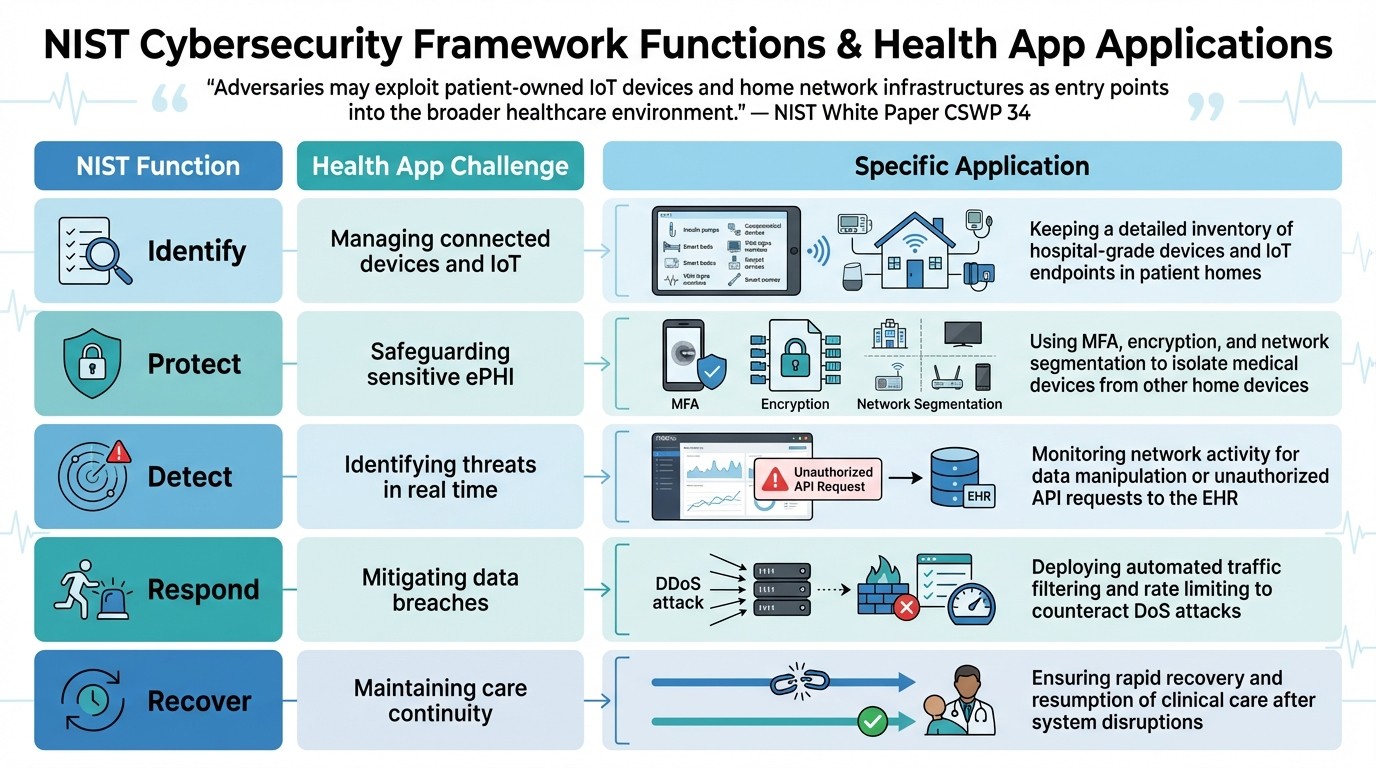
The NIST Cybersecurity Framework (CSF) 2.0 outlines five core functions - Identify, Protect, Detect, Respond, and Recover - designed to tackle the specific challenges faced by health apps. Unlike traditional enterprise systems, health apps often operate in complex environments like Hospital-at-Home setups. These settings combine hospital-grade devices with consumer IoT products, many of which fall outside centralized control [14]. The framework serves as a guide for addressing vulnerabilities in this mixed ecosystem of medical and consumer technologies.
Each function addresses a key area of risk. The Identify function focuses on cataloging every component that interacts with patient data. This includes hospital-grade biometric devices, third-party APIs, and even personal devices owned by patients.
The Protect function demands robust security measures, such as adopting Zero Trust architectures (as outlined in NIST SP 800-207). This involves continuous authentication for all users and devices accessing Electronic Health Records (EHRs). Additionally, network segmentation plays a critical role, isolating medical devices from other home network devices to prevent breaches through compromised IoT products like smart speakers.
"Adversaries may exploit patient-owned IoT devices and home network infrastructures as entry points into the broader healthcare environment." - NIST White Paper CSWP 34
The Detect function emphasizes real-time monitoring to spot anomalies, such as Distributed Denial of Service (DDoS) attacks or unauthorized API activities that could compromise patient data. The Respond function focuses on automated mitigation strategies, such as traffic filtering and rate limiting, to reduce disruptions to essential clinical services. Lastly, the Recover function prioritizes restoring system availability and predictability, ensuring patients continue to receive uninterrupted care.
The table below highlights how these NIST functions address specific challenges and applications in health apps:
NIST Function | Health App Challenge | Specific Application |
|---|---|---|
Identify | Managing connected devices and IoT | Keeping a detailed inventory of hospital-grade devices and IoT endpoints in patient homes |
Protect | Safeguarding sensitive ePHI | Using MFA, encryption, and network segmentation to isolate medical devices from other home devices |
Detect | Identifying threats in real time | Monitoring network activity for data manipulation or unauthorized API requests to the EHR |
Respond | Mitigating data breaches | Deploying automated traffic filtering and rate limiting to counteract DoS attacks |
Recover | Maintaining care continuity | Ensuring rapid recovery and resumption of clinical care after system disruptions |
Getting Ready for 2026 Compliance: A Step-by-Step Plan
The December 2024 Notice of Proposed Rulemaking has set the stage for stricter auditing and technical requirements for health apps by 2026 [15]. With the shift from vague "reasonable and appropriate" standards to clear, time-bound mandates, organizations need to act now. Here's a practical plan to prepare for these changes.
Running a Complete Risk Analysis
Start with a thorough risk analysis of all e-PHI (electronic Protected Health Information) stored, transmitted, or accessed via mobile devices, cloud platforms, and other media [8]. The proposed 2026 rules emphasize maintaining an up-to-date asset inventory and network map that tracks the flow of e-PHI, refreshed at least annually [15]. Identify potential threats - whether natural, human, or environmental - and evaluate their likelihood and potential impact [8].
The new regulations also require annual compliance audits, biannual vulnerability scans, yearly penetration tests, and the ability to restore data and systems within 72 hours [15]. These measures, which were previously considered optional, are now mandatory for nearly all cybersecurity practices [15].
Once risks are identified, implement robust access controls and establish continuous monitoring systems to mitigate vulnerabilities effectively.
Role-Based Access and Continuous Monitoring
Implement Zero Trust principles to enforce role-based access controls, treating every login attempt as potentially untrusted, regardless of its origin [17]. The HHS Office for Civil Rights has increased enforcement efforts, announcing 10 settlements in the first five months of 2025 alone, many of which stemmed from failures in basic risk analysis [17]. Multi-factor authentication (MFA) is now a requirement for all administrative and critical system access under the updated HIPAA Security Rule proposals [17].
For health apps operating in cloud environments, it's crucial to securely configure Identity and Access Management (IAM) policies, manage application-level credentials, and enforce strict authorization measures [16]. Network segmentation is another key strategy - separating clinical and medical device networks from general IT and guest networks can help contain potential breaches and limit lateral movement by attackers [17]. To maintain continuous vigilance, establish a Security Operations Center (SOC) or partner with a Managed Detection and Response (MDR) service to monitor for signs of data exfiltration or unusual access patterns [17].
Conclusion
The NIST Cybersecurity Framework 2.0 introduces a flexible, risk-based approach that’s crucial for health apps navigating today’s complex cybersecurity landscape. With NIST SP 800-66 Rev. 2 aligning HIPAA Security Rule elements to CSF 2.0 subcategories, this framework has become a key resource for meeting compliance requirements and building user confidence [1]. As Jeff Marron, a cybersecurity specialist at NIST, explained:
"The revision is more actionable so that health care organizations can improve their cybersecurity posture and comply with the Security Rule" [1].
The surge in healthcare-related cyberattacks highlights the importance of protecting sensitive data. For health apps managing electronic protected health information, safeguarding the confidentiality, integrity, and availability of this data is non-negotiable. The addition of the "Govern" function in CSF 2.0 emphasizes that cybersecurity is not just an IT issue - it’s a critical component of broader enterprise risk management [2][3]. This makes strong cybersecurity practices both a regulatory requirement and a strategic advantage.
Looking ahead, updates to the IR 8286 series by December 2025 will fully align with CSF 2.0, while tools like SP 800-70r5 will simplify compliance reporting through automation [3]. This framework also addresses emerging technologies that are transforming healthcare, such as AI-powered health tools and IoT devices used in home care [5].
By taking steps like conducting thorough risk assessments and implementing continuous monitoring, health apps can align their technical controls with regulatory standards. Tools like the CSF 2.0 Reference Tool and Quick-Start Guides provide a clear path to updating security measures for 2026 compliance. As NIST emphasizes:
"The CSF does not prescribe how outcomes should be achieved. Rather, it links to online resources that provide additional guidance on practices and controls that could be used to achieve those outcomes" [2].
This flexible, outcome-driven approach allows health apps to customize their security strategies based on their unique risk profiles, all while meeting the rigorous standards of the future.
For apps like Healify, adopting these practices isn’t just about meeting regulations - it’s about earning user trust and safeguarding sensitive health data in an increasingly digital world.
FAQs
What does the new 'Govern' function in NIST CSF 2.0 mean for health app developers?
The updated 'Govern' function in NIST CSF 2.0 places a stronger emphasis on cybersecurity governance, aligning risk management with an organization's broader objectives while promoting accountability. For health app developers, this means establishing clear oversight of cybersecurity efforts, refining how risks are identified and mitigated, and adhering to new governance standards.
This shift underscores the need to weave cybersecurity into the fabric of business strategies - an essential move for health apps managing sensitive data such as biometrics and medical records. Developers must take proactive steps to protect user information, ensuring their operations remain transparent and accountable.
What should small health app developers do to meet NIST and HIPAA security requirements?
To comply with NIST and HIPAA security standards, small health app developers should prioritize a few essential security practices. Start by familiarizing yourself with the NIST Cybersecurity Framework and the latest updates to SP 800-66r2, which offer actionable steps for meeting the HIPAA Security Rule requirements. Regular risk assessments are a must - identify weaknesses, address them promptly, and implement safeguards to secure electronic protected health information (ePHI).
Another critical step is aligning your security protocols with the crosswalk between the HIPAA Security Rule and the NIST framework. This ensures your app includes essential protections like data encryption, access controls, and incident response plans. Staying informed on regulatory changes and updated guidance is key to keeping your app compliant and protecting user data effectively.
Why is multi-factor authentication so important for health apps under the updated NIST guidelines?
Multi-factor authentication (MFA) plays a crucial role in securing health apps by adding an extra layer of protection. This makes it far more difficult for unauthorized individuals to gain access to sensitive health data. It also aligns with the updated NIST Cybersecurity Framework, which prioritizes safeguarding personal information and managing cybersecurity risks effectively.
MFA works by requiring users to confirm their identity through multiple verification methods - like entering a password and then using a code sent to their phone. This significantly lowers the risk of data breaches. For health apps that handle highly sensitive information, such as biometrics or medical records, implementing MFA isn't just a smart move - it’s essential for maintaining user trust and meeting today’s security requirements.
Related Blog Posts
Endlich die Kontrolle über Ihre Gesundheit übernehmen

Endlich die Kontrolle über Ihre Gesundheit übernehmen

Endlich die Kontrolle über Ihre Gesundheit übernehmen




