AI is transforming the security of Remote Patient Monitoring (RPM) systems by addressing key vulnerabilities in data privacy, device connectivity, and healthcare infrastructure. Here's how it works:
- Data Privacy: AI uses encryption methods for wearable health devices to protect sensitive medical data and ensures secure access through advanced techniques like homomorphic encryption and trust management systems.
- Threat Detection: AI models detect anomalies in real time, identifying spoofed devices, forged data, or network attacks with high accuracy.
- Data Integrity: AI and blockchain work together to verify and protect data from tampering, creating immutable records and ensuring compliance with regulations like HIPAA.
- Decentralized Processing: AI processes data locally on edge devices, reducing latency and exposure during transmission.
With RPM systems becoming essential for chronic care and remote health monitoring, AI-driven security ensures patient safety and compliance with strict healthcare regulations.
Telehealth Cybersecurity: Secure Remote Patient Monitoring Ecosystem
sbb-itb-f5765c6
Security Challenges in Remote Patient Monitoring
Remote patient monitoring (RPM) systems face significant security risks that can jeopardize both patient safety and data privacy. The interconnected nature of these devices, paired with outdated healthcare infrastructure, creates vulnerabilities that attackers can exploit. Let’s dive into the key areas where these challenges emerge.
Data Privacy Risks in Healthcare
The shift to digital health records has made medical data a prime target for cybercriminals. This data includes highly personal information - such as chronic conditions and mental health details - which can have devastating consequences if disclosed or altered without authorization. Shockingly, only about 25% of IoT devices and data repositories use encryption [7], leaving much of this sensitive information exposed.
A study in Scientific Reports highlights the gravity of this issue:
"Medical data contains sensitive attributes, and its disclosure and alteration might create life-threatening effects." [3]
Imagine an attacker manipulating vital signs like heart rate. Such tampering could lead doctors to administer incorrect treatments or delay critical care. The risks are amplified by traditional cloud-based storage methods, which centralize Protected Health Information (PHI) in single locations. This setup not only creates a tempting target for hackers but also erodes patient trust, as individuals lose control over who accesses their data and when [4].
Organizations face the added challenge of navigating complex compliance frameworks like HIPAA in the U.S., GDPR in Europe, and India's DPDP Act. Each regulation comes with unique data handling and breach notification requirements, adding layers of complexity to an already fraught system.
Device Connectivity and Network Vulnerabilities
The growing number of connected medical devices has significantly expanded the attack surface. By 2025, there will be an estimated 41.6 billion IoT devices generating 79.4 zettabytes of data [7]. Every wearable, implantable monitor, or home health device becomes a potential entry point for cyberattacks.
Unfortunately, many RPM devices are constrained by design. With limited power, storage, and processing capabilities, these devices often can't support robust security measures. The variety of communication protocols - like Wi-Fi, Bluetooth, and LoRa - further complicates the task of maintaining consistent security across a network.
Attackers exploit these vulnerabilities through methods such as:
- Device spoofing: Impersonating legitimate devices to inject false data.
- Data forgery: Altering physiological readings to mislead healthcare providers.
- Signal injection: Adding noise to bypass anomaly detection systems.
As noted in Scientific Reports:
"Traditional security mechanisms lack dynamic adaptability to streaming multimodal physiological data, making them ineffective in safeguarding H-IoT devices against evolving threats and tampering." [6]
Network dependency adds another layer of risk. Many real-time health monitoring systems rely on cloud processing, which can lead to dangerous delays or gaps in care during connectivity issues. For instance, a dropped connection during a cardiac event could prevent timely intervention, with potentially life-altering consequences.
Healthcare Infrastructure Vulnerabilities
Security challenges extend beyond individual devices to systemic weaknesses in healthcare infrastructure. The consolidation of healthcare providers, payers, and pharmacy benefit managers under a few large corporations has created massive single points of failure. When these entities are compromised, the effects can ripple across entire regions.
One stark example is the June 2024 cyberattack on Synnovis, a pathology services provider for the UK National Health Service. This breach caused one patient death and injuries to 14 others [8]. Similarly, the early 2025 breach of Oracle Cloud's Electronic Medical Record system exposed over 6 million medical records, proving that even major cloud providers are not immune to large-scale attacks [8].
Legacy medical devices further compound the problem. Many of these devices were built before modern security standards became the norm, and new FDA security requirements often don’t apply to older models [8]. Without updates or patches, these devices remain vulnerable, creating weak links in the system.
The healthcare industry’s lack of investment in resilient infrastructure exacerbates these issues. Organizations often struggle to switch vendors during outages or attacks, as Richard Staynings, Chief Security Strategist at Cylera, explains:
"The industry is simply unprepared to quickly switch out one vendor for another in times of difficulty, as the Change Healthcare attack and many other such attacks have proven." [8]
Fragmented health information systems across providers make it nearly impossible to implement unified security protocols. This is particularly concerning given that 90% of the $4.9 trillion in annual U.S. healthcare spending is tied to individuals with chronic and mental health conditions [8] - the very population that depends most on RPM systems. Unfortunately, the rush to adopt these technologies often prioritizes speed over security, leaving critical gaps unaddressed.
How AI Improves Remote Patient Data Security
Artificial intelligence strengthens the security of remote patient monitoring (RPM) systems by focusing on smarter encryption, continuous threat monitoring, and automated data validation. These capabilities work together to safeguard patient data from the moment it’s collected by sensors to when it reaches healthcare providers. By addressing vulnerabilities head-on, AI ensures a stronger, more adaptive defense against potential threats.
AI-Powered Data Encryption and Access Control
AI has revolutionized data encryption for RPM systems, making it possible to process encrypted data without compromising security. Techniques like Homomorphic Encryption (e.g., the Paillier scheme) and Lightweight Elliptic Curve Cryptography (ECC) allow secure data analysis and authentication without overburdening system resources. For instance, hospitals can use AI to analyze heart rate data while keeping the actual numbers encrypted.
In March 2026, researchers tested a hybrid security model called the CNN-TMS-ECC framework on medical sensor networks. This system achieved 95% accuracy in detecting threats while meeting the low-power requirements of devices with limited resources. As noted in Scientific Reports (2026):
"The CNN-TMS-ECC model provides a safe, low-latency, and energy-efficient security solution for medical devices, enabling effective communication and real-time intrusion detection in smart healthcare systems."
AI also enhances access control through Trust Management Systems (TMS), which dynamically calculate trust scores for devices based on their behavior, interaction history, and likelihood of anomalies. A Trust-Aware Adaptive Controller (TAC) monitors these scores in real time, isolating or limiting devices that show suspicious activity.
In February 2025, the DeW-IoMT Framework showcased this approach by using a "Roof Layer" gateway to manage role-based access control and AES encryption before data reached cloud storage. This decentralized system reduced response time by 74.61% and energy use by 38.78% compared to traditional cloud-based methods [3].
Real-Time Threat Detection and Anomaly Recognition
Beyond encryption, AI plays a critical role in identifying threats as they happen. Hybrid CNN-LSTM models analyze real-time signals like ECG and oxygen saturation to detect spoofed devices, forged data, or injected signals with 98.7% accuracy.
Edge-AI technology processes this analysis locally on devices such as NVIDIA Jetson Nano or Raspberry Pi, cutting inference latency by 52% compared to cloud-based setups [5]. For example, in August 2025, researchers tested a CNN-LSTM-VAE framework on the MIT-BIH Arrhythmia dataset. This system achieved 98.7% accuracy in detecting anomalies while maintaining latency under 160 milliseconds on edge hardware [6]. The framework’s Trust-Aware Controller flagged sensors with frequent anomalies or irregular timestamps, isolating them automatically.
AI-powered Intrusion Detection Systems (IDS) add another layer of protection by monitoring network traffic for attacks like man-in-the-middle, replay, and eavesdropping. These systems have achieved up to 95% accuracy in identifying network anomalies - outperforming traditional models by 8–10% [9]. According to IEEE Access:
"AI-powered threat intelligence enhances RPM security considerably due to its ability of continuous monitoring, adaptive defense mechanisms, and early detection of threats."
This real-time monitoring directly addresses vulnerabilities in connectivity and network security, making RPM systems more resilient.
Data Integrity Verification with AI
Ensuring data integrity during transmission is vital, and AI provides multiple tools to prevent tampering or corruption.
Variational Autoencoders (VAEs) play a key role by reconstructing input signals and measuring reconstruction errors. Any significant deviation between the original input and its reconstruction can indicate tampering or sensor malfunction [6].
Combining blockchain with AI further strengthens data integrity. Blockchain creates an immutable audit trail by storing AI-generated summaries and hashes on permissioned blockchains using a Proof-of-Authority consensus. In 2025, an Edge-AI framework that paired CNN-LSTM models with blockchain achieved 91.9% accuracy in real-time anomaly detection with an average latency of 118 milliseconds [5]. As highlighted in Scientific Reports (2025):
"Blockchain technology provides immutable and verifiable logging of anomaly events, ensuring accountability and facilitating compliance with clinical data audit requirements."
AI also uses spatial-temporal anomaly detection to analyze not just individual data points but their sequence and inter-sensor relationships. For example, a sudden spike in blood pressure that doesn’t align with heart rate changes would be flagged immediately. Smart contracts further automate consent management by ensuring data access complies with clinical and regulatory guidelines [5][4]. Together, these AI-driven methods have achieved data preservation rates exceeding 99.2% in real-world tests [6].
Blockchain and AI for RPM Security
How AI and Blockchain Secure Remote Patient Monitoring Systems
Immutable Data Records with Blockchain
Blockchain ensures patient data remains unaltered by storing cryptographic hashes on a distributed ledger. This approach prevents modifications after data is recorded, securing the transaction history.
In remote patient monitoring (RPM) systems, blockchain often uses permissioned or consortium models, such as Hyperledger Fabric. These models restrict consensus to verified healthcare entities like hospitals, clinics, and approved providers. A notable example is EHRGuard, introduced in 2025. This system integrates IoMT (Internet of Medical Things) sensors with a permissioned blockchain, logging sensor data as transactions. Authorized doctors act as light nodes for real-time monitoring, while the blockchain safeguards against tampering [10].
Blockchain complements AI's real-time threat detection by ensuring any changes to data are permanently recorded. To avoid overloading the ledger, hybrid storage solutions are common. Large medical files are stored off-chain using tools like the InterPlanetary File System (IPFS), while only metadata and cryptographic validation hashes are kept on the blockchain [10]. As highlighted in Scientific Reports:
"Blockchain technology has emerged as a promising solution to enhance privacy and security, particularly in sensitive areas such as medical data within the Internet of Things." [10]
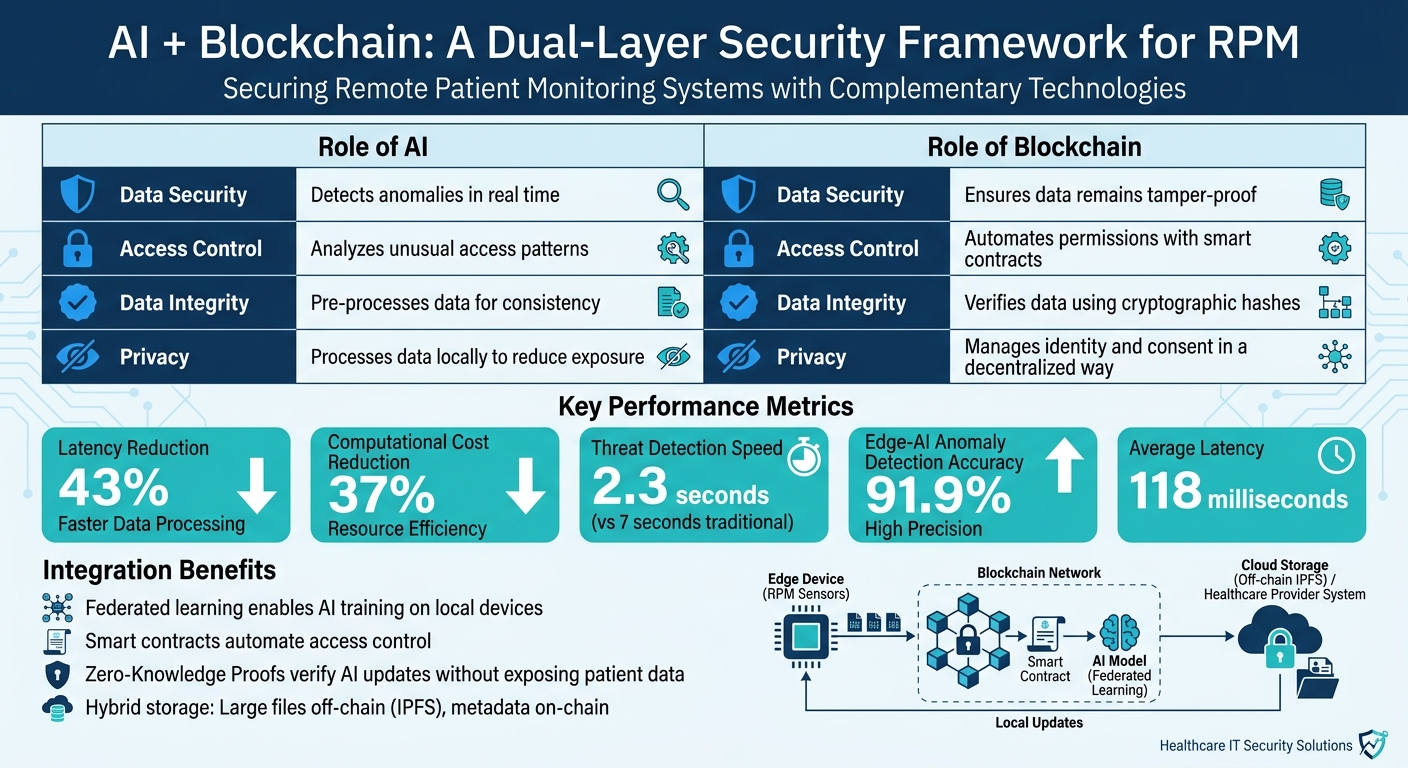
How Blockchain and AI Work Together
The combination of blockchain and AI creates a robust security framework, addressing both immediate threats and long-term data integrity. AI focuses on real-time tasks like anomaly detection and health risk alerts, data quality checks, and intrusion identification, while blockchain ensures a permanent audit trail of these activities.
Federated learning plays a key role by enabling AI training on local edge devices. Only encrypted model updates are stored on the blockchain, cutting latency by 43% and computational costs by 37% [11].
Smart contracts add another layer of security by automating access control and consent management, ensuring only authorized individuals can access specific data streams. Meanwhile, Zero-Knowledge Proofs allow healthcare providers to verify AI model updates without exposing sensitive patient information. Additionally, edge-based anomaly detection within these blockchain-AI systems can identify security threats in approximately 2.3 seconds, significantly faster than the 7-second average of traditional systems [11].
| Feature | Role of AI | Role of Blockchain |
|---|---|---|
| Data Security | Detects anomalies in real time | Ensures data remains tamper-proof |
| Access Control | Analyzes unusual access patterns | Automates permissions with smart contracts |
| Data Integrity | Pre-processes data for consistency | Verifies data using cryptographic hashes |
| Privacy | Processes data locally to reduce exposure | Manages identity and consent in a decentralized way |
Together, these technologies enhance data security and compliance, creating a layered framework that addresses both technical and regulatory demands. This synergy between blockchain and AI is shaping the future of secure healthcare systems.
Regulations and AI Compliance in Remote Patient Monitoring
Remote Patient Monitoring (RPM) devices, often categorized as Class II and requiring 510(k) clearance, must adhere to strict HIPAA and FDA standards. AI plays a key role in ensuring compliance by automating security measures and maintaining detailed audit logs. Non-compliance with HIPAA regulations can result in hefty penalties ranging from thousands to millions of dollars, depending on the severity of the violation [2]. This level of regulatory scrutiny highlights the importance of integrating AI-driven compliance tools.
How AI Supports HIPAA Compliance
AI simplifies HIPAA compliance by automating critical safeguards, such as end-to-end encryption for data at rest, in transit, and during storage [2]. It also creates detailed audit trails, capturing information like data inputs, algorithm versions, and access logs. Techniques like federated learning improve AI models without centralizing sensitive data, minimizing risks [2][4][1].
AI-powered monitoring systems are particularly effective at identifying unusual patterns in data access, unauthorized changes to algorithms, or suspicious system activity. These tools offer real-time breach detection capabilities that surpass traditional compliance methods [2]. Additionally, AI enforces HIPAA’s “minimum necessary” rule by ensuring only the required physiological, behavioral, or environmental data is collected for specific clinical purposes [2].
To address concerns like algorithm bias and data usage, healthcare providers must update Business Associate Agreements (BAAs) with AI vendors [2]. For example, HIPAA-compliant hosting solutions typically start at around $229 per month [2]. As the HIPAA Partners Team explains:
"The investment in robust compliance programs pays dividends through reduced regulatory risk, improved patient trust, and enhanced care quality." [2]
| HIPAA Requirement | AI Support Mechanism |
|---|---|
| Technical Safeguards | End-to-end encryption and automated multi-factor authentication [2] |
| Audit Controls | Automated logs detailing data inputs and algorithm versions [2] |
| Integrity | Blockchain anchoring and AI-based anomaly detection to prevent tampering [4][1] |
| Transmission Security | Secure VPNs and AI-monitored network segmentation to protect PHI [2] |
| Patient Rights | Explainable AI models that clarify data usage for patients [2] |
Transparency and Accountability in AI Governance
Regulatory standards emphasize the need for transparency and accountability in AI systems. Both the FDA and HIPAA require that AI-generated clinical insights be understandable to healthcare providers [13]. This has led to the rise of Explainable AI (XAI), which provides clear, interpretable insights, making it easier for clinical teams to trust and audit AI recommendations.
Maintaining human oversight is equally critical. AI should function as an "augmented intelligence" tool, filtering alerts to highlight critical issues while leaving final decisions to clinicians [12]. This approach reduces alert fatigue without compromising accountability. As HealthManagement.org notes:
"Adherence to HIPAA, TEFCA and FDA standards ensures privacy, security and explainability of AI models - crucial for provider trust and patient safety." [13]
When combined with blockchain, AI can generate tamper-evident logs of physiological inferences and alerts using cryptographic hashes [4]. Smart contracts further enhance compliance by automating consent management and alert workflows [4]. Dr. Isabelle Laurent from the School of Computational Biology at Université Internationale de Lyon explains:
"The design... strengthens provenance and auditability, and enable compliant data minimization." [4]
Healthcare organizations should prioritize explainability when selecting AI vendors for RPM. Models must be auditable and trusted by clinical teams [13]. Routine audits, role-based access controls, and embedding AI insights directly into EHR dashboards can help protect patient data while seamlessly integrating into existing clinical workflows, avoiding extra documentation burdens.
Conclusion
AI is reshaping how healthcare organizations protect remote patient monitoring systems from the ever-changing landscape of cyber threats. By integrating advanced technologies like real-time anomaly detection, federated learning, and blockchain, AI builds a multi-layered defense system that surpasses traditional approaches. These advances have been shown to significantly cut latency and response times, offering a faster and more effective security solution [5][3].
One major advantage lies in the move toward decentralized intelligence, which keeps sensitive patient data closer to its source, limiting vulnerabilities during transmission. Techniques like homomorphic encryption allow AI to process encrypted data securely, adding just an 8.7% latency overhead while ensuring raw data remains protected [5]. Additionally, AI-driven trust scoring systems monitor device behavior in real time, isolating compromised sensors before they can cause harm [6]. This combination of privacy and proactive defense forms a strong technical backbone for balancing innovation with risk management.
As Ana Wagner Oroz, a Healthcare Innovation Writer, puts it:
"The convergence of artificial intelligence and remote patient monitoring (RPM) promises a paradigm shift in modern healthcare... but this digital transformation is not without its risks" [14].
AI addresses these risks by offering continuous monitoring and adaptive security measures.
Healthcare providers that adopt AI-driven security frameworks position themselves as leaders in the era of Healthcare 5.0. Features like explainable AI, dynamic trust management, and blockchain-based audit trails ensure secure and compliant remote care, building trust among patients. With the Internet of Medical Things (IoMT) market expanding rapidly, investing in robust AI security systems is no longer optional - it's essential for scaling remote patient monitoring effectively.
FAQs
How can AI stop fake RPM devices from sending bad data?
AI plays a critical role in maintaining the reliability of remote patient monitoring (RPM) systems by stopping fake devices from sending inaccurate data. It uses real-time anomaly detection powered by edge AI models to check the authenticity of data before it’s transmitted. Additionally, techniques like federated learning and blockchain-based tamper-evident logging help ensure data remains secure and trustworthy, reinforcing the integrity of RPM systems.
Does edge AI keep my health data off the cloud?
Edge AI processes your health data directly on local devices, such as smartphones or wearables, rather than relying heavily on cloud servers. By doing so, it helps protect your privacy by keeping sensitive information closer to you and limiting its exposure to outside networks.
What’s the simplest way to use blockchain for HIPAA-ready RPM logs?
The easiest approach is to implement a permissioned blockchain system, such as Hyperledger Fabric. This type of system provides tamper-evident logging, ensures secure management of patient consent, and enables safe data sharing between institutions. These capabilities align with HIPAA compliance standards for remote patient monitoring (RPM) systems.